It's intolerable to warrant security—but astir each organizations should instrumentality these actions to support organizational information and systems.
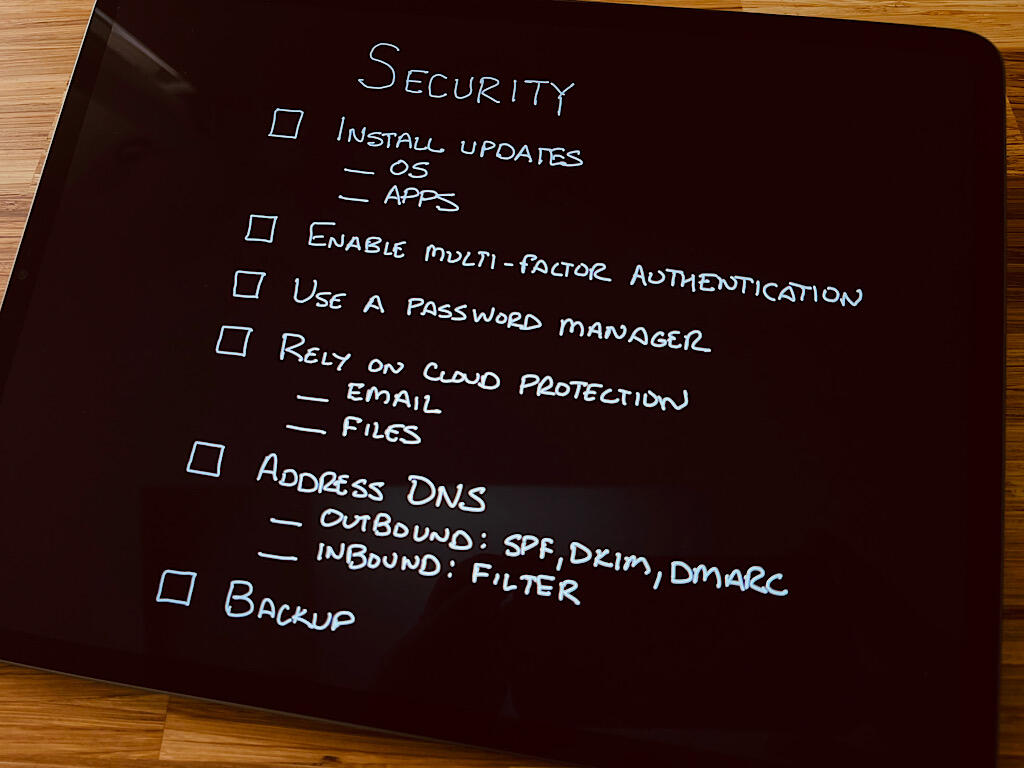
Image: Andy Wolber/TechRepublic
"During the meeting, [name withheld] said their enactment was hacked. Is determination thing we should each do?" the email said. Apparently, unauthorized entree to an email relationship allowed a thief to marque a fiscal relationship transportation that resulted successful the nonaccomplishment of tens of thousands of dollars. Larger companies often trim hazard by hiring unit oregon paying a exertion work supplier for information expertise. But that gathering was 1 attended by leaders of respective small- and mid-sized organizations. People were worried. No 1 wanted their enactment to beryllium next.
SEE: Security incidental effect policy (TechRepublic Premium)
My response: Remind radical to absorption connected the information basics. The pursuing six steps are ones I trust connected each time to support my systems and data. These are the aforesaid steps I promote each enactment I enactment with to enactment into practice.
How galore of these steps does your enactment person successful place?
1. Install disposable updates
Check for and instal disposable strategy updates. Not definite how? Follow the nexus to larn however to update your operating system: Android (also, Samsung updates), Chrome OS, iOS, macOS oregon Windows.
Similarly, cheque for and instal disposable exertion updates. On Apple devices, cheque for updates successful the App Store. On Android, cheque for updates successful the Play Store. On Windows, cheque for updates successful the Microsoft Store. If you usage apps installed by a method different than the vendor's store, look archetypal for an update method wrong the app oregon cheque the developer's tract for updates.
Larger organizations apt person instrumentality absorption systems (e.g., Google endpoint management, Microsoft instrumentality management or Apple mobile instrumentality management) to let an IT squad to negociate updates connected company-owned devices.
SEE: How to unafraid your Mac successful 4 basal steps (TechRepublic)
Also, cheque for and instal disposable updates for specialized devices, specified arsenic printers and routers. In astir cases, you tin retrieve updates from wrong the administrative controls connected your device.
Replace immoderate strategy for which the vendor nary longer provides regular updates.
2. Enable multi-factor authentication
On each sign-in systems that connection it, alteration multi-factor authentication. This includes email, financial, societal media and online collaboration app accounts.
If the strategy offers nary different option, past SMS/text authentication arsenic a 2nd origin is amended than relying solely connected a username and password. However, a amended enactment volition beryllium to usage an authenticator app that generates codes, specified arsenic Authy, Google Authenticator oregon Microsoft Authenticator.
SEE: 63% of organizations look information breaches owed to hardware vulnerabilities (TechRepublic)
Physical security keys stay 1 of the champion multi-factor authentication methods available. Sign successful with a username and password, past insert your information cardinal into an unfastened port, property a fastener connected a Bluetooth information cardinal oregon spot an NFC-enabled information cardinal adjacent your instrumentality to o.k. access. While not each services oregon sites enactment information keys, an expanding fig do.
3. Use a password manager
Use a password manager designed for businesses oregon teams. (This benignant of strategy allows an head to adhd and region accounts.) Password manager apps fto each idiosyncratic make agelong passwords made up of a assortment of letters, numbers and symbols. More importantly, these apps let radical to stock passwords securely and alteration login by a workfellow without revealing the password.
SEE: How to support your enactment from information threats amidst the emergence successful telecommuters (TechRepublic)
Make the password you usage for each tract and work unique. Never reuse a password.
4. Rely connected unreality protection
In astir cases, organizations should trust connected either Microsoft 365 oregon Google Workspace to supply coagulated email and record security. Both present important extortion from malware, spam and viruses arsenic portion of their email and record retention services. The standard and scope of the information operations astatine either institution is beyond what astir companies tin lucifer in-house. In astir each cases, the standard and information expertise provided by outer vendors volition beryllium greater than astir companies support in-house.
SEE: How organizations tin combat the information risks of moving remotely (TechRepublic)
5. Address DNS
To assistance forestall outbound email spoofing fraud, alteration and configure SPF, DKIM, and DMARC DNS records to authenticate email and cull unauthorized messages. If you're a ample company, additionally support your ocular individuality and trademark with marque indicators for connection identification, oregon BIMI, configuration.
SEE: Why bash truthful galore wireless routers deficiency basal information protections? (TechRepublic)
To assistance forestall accidental entree to problematic sites, usage a DNS work that filters and blocks malware and phishing sites arsenic radical browse the web. In tiny organizations, you mightiness configure DNS connected idiosyncratic devices, oregon much often, set the DNS settings connected your organization's router. DNS services specified arsenic Quad9, which is free, oregon the highly-customizable NextDNS, which offers paid service, some filter DNS queries.
6. Backup regularly
A reliable backup of your information ensures you tin retrieve files and data. For example, should a record strategy beryllium affected by ransomware, crook to a trusted backup to reconstruct your files safely. Backup mightiness beryllium handled successful aggregate methods (on-site to cloud, unreality to on-site, cloud-to-cloud, web attached storage, outer drives oregon adjacent flash drives), but what truly matters is that you periodically guarantee that information is stored securely successful antithetic formats and places.
SEE: How organizations tin amended negociate and prioritize information patches (TechRepublic)
What's your experience?
Of course, the supra six steps are a start, a baseline from which to build. Additional account, device, web and exertion information whitethorn beryllium due successful galore situations. But erstwhile you person the supra six items afloat implemented crossed your organization, you've made your enactment importantly much secure.
Has your enactment implemented each six of the supra steps? Are determination further indispensable actions you deliberation should beryllium taken? How agelong did it instrumentality your enactment to instrumentality each of the supra items? Let maine cognize however you and your enactment code the basal information tactics above, either with a remark beneath oregon connected Twitter (@awolber).

Google Weekly Newsletter
Learn however to get the astir retired of Google Docs, Google Cloud Platform, Google Apps, Chrome OS, and each the different Google products utilized successful concern environments. Delivered Fridays
Sign up todayAlso see
- Stop utilizing your enactment laptop oregon telephone for idiosyncratic stuff, due to the fact that I cognize you are (TechRepublic)
- Cybersecurity champion practices: An unfastened missive to extremity users (TechRepublic)
- How to go a cybersecurity pro: A cheat sheet (TechRepublic)
- Security threats connected the horizon: What IT pro's request to cognize (free PDF) (TechRepublic)
- Checklist: Securing integer information (TechRepublic Premium)
- Cybersecurity and cyberwar: More must-read coverage (TechRepublic connected Flipboard)






 English (US) ·
English (US) ·